The Seven of Hearts
Security research, CTF writeups, and hacking adventures
Metasploitable 3
The Seven of Hearts
For this one I used SSH with the Administrator account with the password that I guessed for another flag/card.
I remembered there was a flag in the C:\inetpub\wwwroot folder and went to take a look at the folder:
root@igor-kali:~/metasploitable3# ssh Administrator@10.20.10.23
Administrator@10.20.10.23’s password:
Last login: Sat Dec 17 12:41:58 2016 from 10.20.10.18
\-sh-4.3$ pwd
/cygdrive/c/Users/Administrator
\-sh-4.3$ cd ../../inetpub
\-sh-4.3$ pwd
/cygdrive/c/inetpub
\-sh-4.3$ cd wwwroot
\-sh-4.3$ ls
aspnet_client caidao.asp hahaha.jpg index.html **seven_of_hearts.html** six_of_diamonds.zip welcome.png
I used Burp Suite to intercept the response with the whole URL generated by the JavaScript embedded in the HTML file
[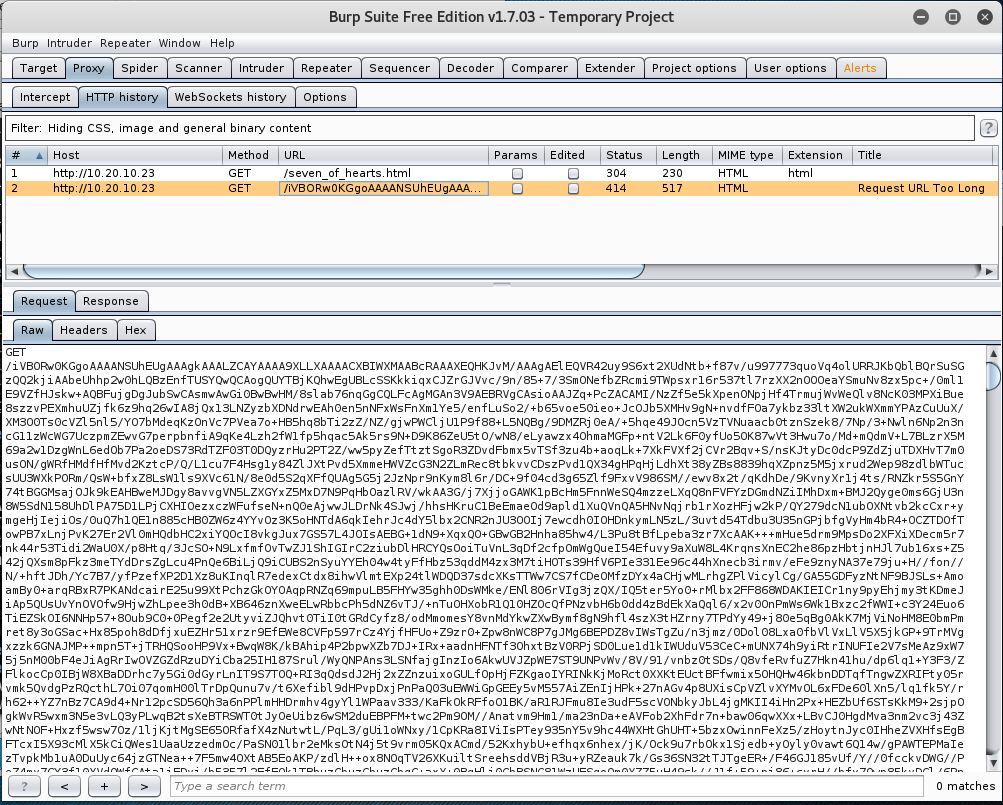](/assets/images/seven_of_hearts-url.jpg)
Burp Suite showing base64 URL
I saved the output to text file in my system and ran a quick perl script with a regex to extract only the base64 data
```bash
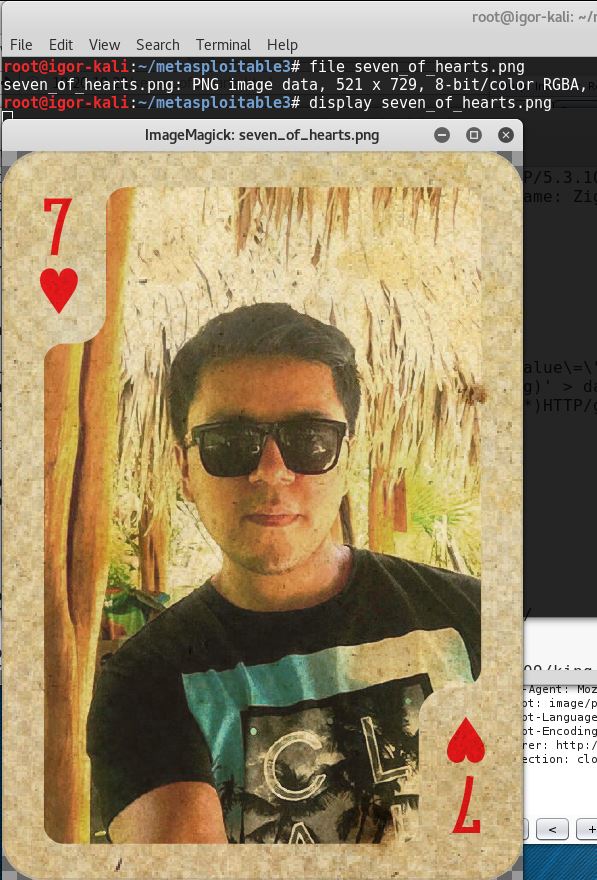
root@igor-kali:~/metasploitable3# cat seven_of_hearts2.url | perl -ne 'print $1 if(/GET \/(.\*)HTTP/g)' > seven_of_hearts.b64
*and then decoded the base64 string to binary*
root@igor-kali:~/metasploitable3# cat seven_of_hearts.b64 | base64 -d > seven_of_hearts.png
base64: invalid input
Even though it gave me an invalid input message it still did it
root@igor-kali:~/metasploitable3# file seven_of_hearts.png
seven_of_hearts.png: PNG image data, 521 x 729, 8-bit/color RGBA, non-interlaced
Johnny Bravo?
← Back to all posts